I’m not going to lie, when I start my day and I see 10 Dependabot PRs open in the project, I just want to close the laptop and go for a walk. And I have the feeling that, like me, many other developers feel the same way, because I keep seeing Dependabot PRs sit open in projects for weeks. Nobody wants to read the changelog, check the dependencies, look for breaking changes, and still risk shipping a regression because they missed an important line buried in the notes.
In the age of AI and automation, we can definitely get some help with this.
This is what my colleague Fritz
suggested. We were watching Dependabot PRs pile up and figured the real pain
point was that people were lacking the information they needed to merge with
confidence. So I used Claude’s skill-creator to build a
skill that gives me exactly that:
a short summary of the changes, the risk, and a recommendation: can I merge,
or do I need to look more carefully myself?
A Dependabot PR review skill
You point the skill at a Dependabot PR or at the whole repo and it gives you back the one thing the PR description never tells you: should I merge this, and if not, why not?
It works in two modes:
- Single-PR mode — paste a Dependabot PR URL and you get a full review for that one PR.
- Audit mode — ask it to “review all open dependabot PRs” and it
discovers every open Dependabot PR in the repo with
gh, analyzes them one by one, and produces a single triage report.
For each PR, the skill does roughly what a careful human would do, just faster and without getting bored:
- Reads the PR diff to figure out the gem name, the old and new version, and whether the bump is patch, minor, or major.
- Pulls the changelog between those two versions from GitHub
releases,
CHANGELOG.md, or RubyGems and only keeps the parts that matter: breaking changes, deprecations, security fixes, notable behaviour changes. The release-notes-style noise gets stripped out. - Greps the codebase to see where the gem is actually used. A bump to a gem that lives in three test files is a very different story from a bump to a gem that runs in your payment flow, and the skill calls that out.
- Hands you a verdict in one of four buckets:
Merge— safe, low riskVerify— looks safe but here are the specific things to check firstInvestigate— needs human judgment, here’s whyHold— there are breaking changes, you’ll need code work before merging
In audit mode you get all of that as a summary table at the top: PR
number, gem, bump (7.2.4 → 8.0.10), type, age, verdict, and a “why”,
sorted worklist style: Merge first, then Verify, Investigate,
Hold.
What the output actually looks like
Here’s a trimmed example of what audit mode prints back into the chat for a repo with a handful of open Dependabot PRs:
Found 5 open Dependabot PRs. Analyzing each now…
| # | Gem | Bump | Type | Age | Verdict | Why |
|-------|----------------|-----------------|----------|-----|-------------|--------------------------------------|
| #9170 | rubocop | 1.65.0 → 1.68.0 | minor | 12d | Merge | dev-only, no breaking changes |
| #9168 | sidekiq | 7.2.4 → 7.3.1 | minor | 6d | Verify | check Redis 6.2+ in production |
| #9165 | aws-sdk-s3 | 1.143 → 1.150 | minor | 21d | Verify | new default checksum algorithm |
| #9159 | devise | 4.9.3 → 4.9.4 | patch | 3d | Merge | patch, safe to merge |
| #9142 | rails | 7.2.4 → 8.0.10 | major | 30d | Hold | breaking: deprecated Active Job APIs |
And then for each PR, a per-PR section with the changelog highlights, the files in your codebase that touch that gem, and the reasoning behind the verdict so you can scan the table for the easy wins.
Posting the review back to the PR
The chat transcript is not where teams review code, so after the review is done, the skill asks if you want to post it as a comment on the PR. Nothing gets posted without an explicit yes.
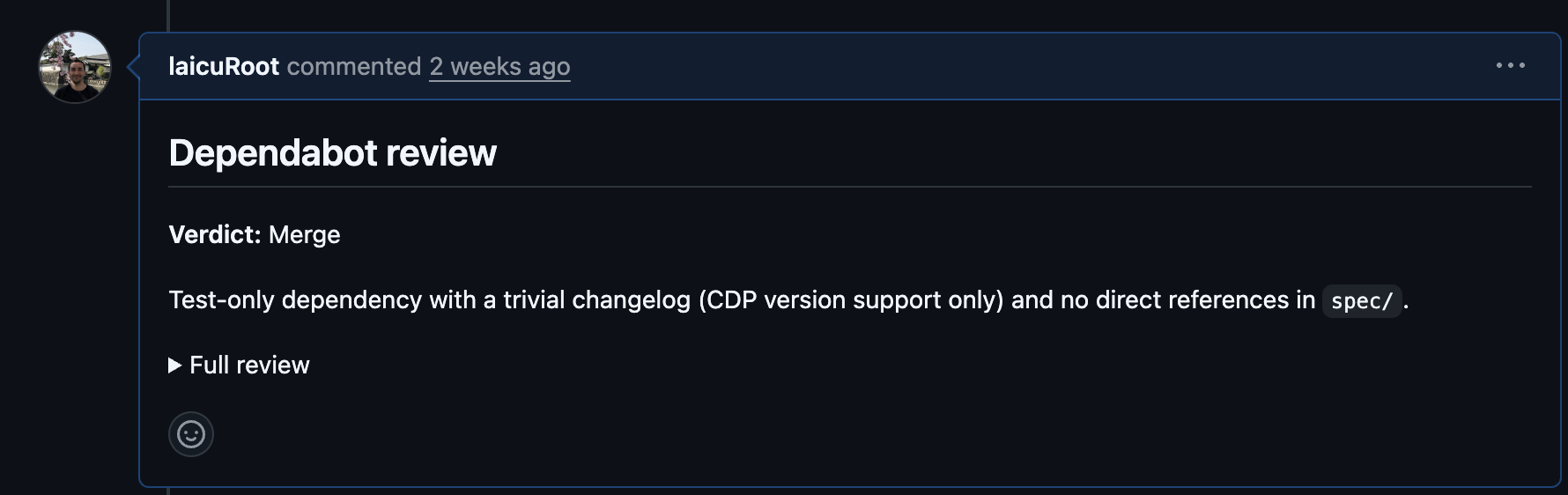
The comment uses a collapsible <details> block, with the verdict and a
one-line reason above the fold so a teammate scrolling the timeline can
triage without expanding, and the full review tucked underneath. There’s
also an invisible marker in the comment, so if you re-run the audit a
week later, it can detect its own previous comments and skip PRs that
already have a review instead of spamming duplicates.
Give it a try
Curious about the skill? Check it out here. If you have any improvements or feedback, please open an issue or pull request. We love feedback!